Every organisation I’ve spoken to over the last few months has hit the same wall. They’ve built agents on Foundry, spun up a few in Copilot Studio, maybe even got a custom Python agent running somewhere on a VM that nobody quite remembers deploying. And now the questions are rolling in: how many agents do we actually have? What data can they access? Who’s responsible for them? Is anyone monitoring what they’re doing?
The agent sprawl is real, and Microsoft Agent 365 is Microsoft’s answer. Going GA on May 1 at $15 per user per month, it’s a unified control plane that treats AI agents like digital users, with the same governance, compliance, and security tooling you already use for your human workforce. Let’s dive in!
In English Please?
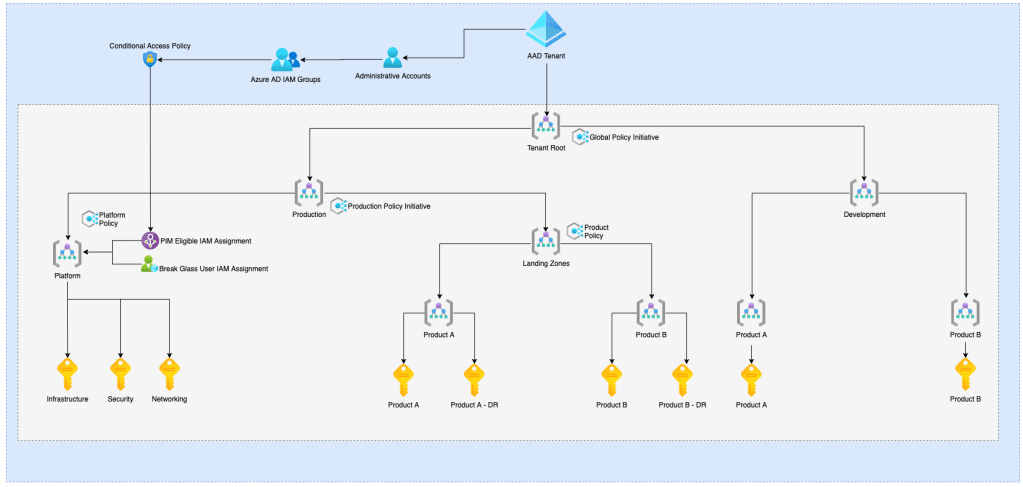
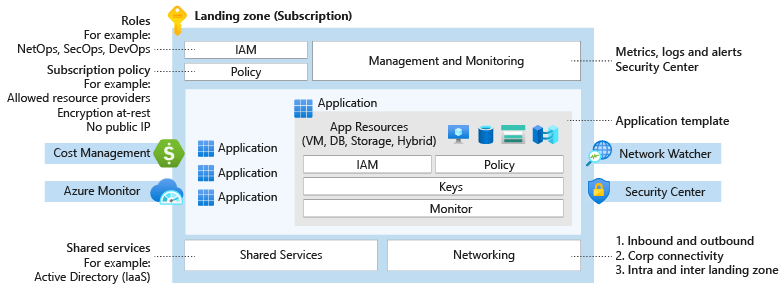
Agent 365 sits above your agent platforms. It doesn’t build or host agents. That’s what Foundry, Copilot Studio, and your own code are for. Instead, it provides a single pane of glass for discovering, governing, securing, and monitoring every agent in your tenant, regardless of where it was built or where it runs.
Think of it as the equivalent of what Entra ID does for human identities, but for AI agents. Every agent gets registered, policies are applied, compliance is enforced, and IT has full visibility. Whether you have 5 agents or 500, Agent 365 ensures they all follow the same rules.
The platform is organised around five pillars:
- Registry: a centralised inventory of every agent in your tenant
- Access Control: identity, conditional access, and lifecycle management via Entra Agent ID
- Visualization: dashboards, agent maps, and usage analytics
- Interoperability: governed access to M365 workloads via MCP servers
- Security: threat protection via Defender, data security via Purview
If you’ve read my previous post on Entra Agent ID, Agent 365 is the governance layer that sits on top of it. Entra gives agents their identity; Agent 365 tells them what they’re allowed to do and watches what they actually do.
The Registry: Finding Your Shadow Agents
First cab off the rank, the Agent Registry. This is accessible from the Microsoft 365 Admin Center under Agents > All Agents, and it’s genuinely eye-opening.
The registry surfaces every agent in your tenant: Microsoft-built, partner-built, organisation-built, and critically, agents that nobody seems to own. For each agent you get:
- Status and availability
- Usage metrics (sessions, active users)
- Exception rates
- Last updated date
- A Risks column that aggregates high-severity alerts from Entra, Purview, and Defender
That last column is gold. At a glance, you can see which agents are generating security alerts and need immediate attention.
There are a few admin capabilities I want to highlight:
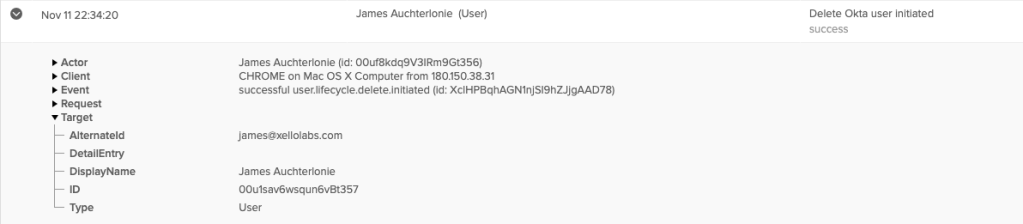
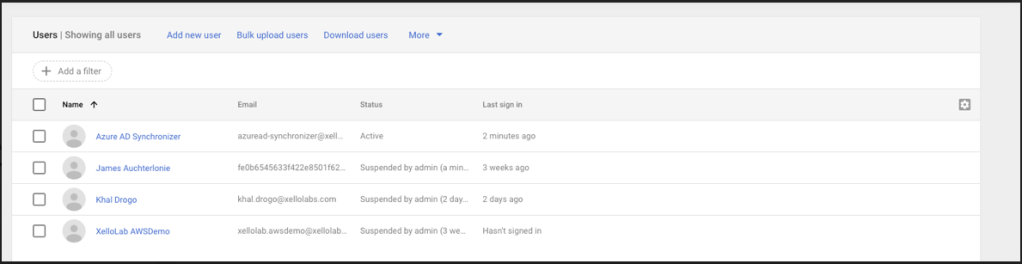
Ownerless agent detection identifies agents whose creator has left the organisation. I’ve heard this from multiple customers. Agents still running months after their creator moved on, with nobody sure what they do or what data they access. Agent 365 flags these automatically and lets you reassign ownership or retire them.
Rules-based lifecycle policies let you automatically expire agents unused for 90 days, flag ownerless agents, or block agents marked as risky. Set it and forget it.
Export to Excel is simple, but critical for audit and compliance reporting. When your auditor asks “show me every AI agent in your environment,” you can hand them a spreadsheet in about three clicks.
The registry is also accessible programmatically via the Microsoft Graph API (currently in preview), using GET packages and GET package details endpoints. If you want to build your own dashboards or integrate agent inventory into your CMDB, that’s your path.
A word of caution though. As Jared Matfess from AvePoint noted after hands-on testing, the registry currently only surfaces published agents. In his tenant, Agent 365 showed 2 agents while the Power Platform admin center listed 47 in development. That’s a significant visibility gap for governance purposes. Third-party agent discovery is also manual; there’s no auto-discovery for agents running outside the Microsoft ecosystem. The vision is a complete inventory; the reality today is a partial one. Worth keeping in mind as you evaluate.
Governance with Purview: DLP, Retention, and the Risky Agents Template
This is where Agent 365 gets seriously interesting for compliance teams. It integrates directly with Microsoft Purview, and the coverage is comprehensive:
| Purview Capability | Supported |
|---|---|
| Data Loss Prevention (DLP) | Yes |
| Sensitivity Labels | Yes |
| Insider Risk Management | Yes |
| Communication Compliance | Yes |
| eDiscovery | Yes |
| Data Lifecycle Management (retention) | Yes |
| DSPM for AI (preview) | Yes |
| Compliance Manager | Yes |
| Auditing | Yes |
A few things that stand out:
DLP for agents: You can include agent instances in DLP policies just like users. Blocks and audits apply to agent-to-human and human-to-agent interactions across Teams, OneDrive/SharePoint, and email. If an agent tries to share a document marked “Highly Confidential” with an external user, DLP catches it. Same rules you already have for your human users, now applied to your AI agents.
The “Risky Agents” template: Insider Risk Management now has a dedicated policy template for AI agents. It detects agents exposed to risky prompts, agents generating sensitive responses, accessing priority SharePoint files, accessing risky websites, sharing files outside the organisation, and anomalous activity patterns. In my opinion, this is one of the most practical features in the entire platform. It takes the insider risk framework you already know and extends it to agents.
eDiscovery for agent interactions: Agent instances are searchable as mailbox sources. If legal needs to produce agent conversations for a matter, it works the same way as eDiscovering a user’s mailbox. This sounds boring until your legal team asks for it and you’re glad it exists.
Retention policies: Automatic retain-or-delete policies for agent interactions. Set your retention period, and Agent 365 handles it. Critical for organisations operating under regulatory retention requirements.
Threat Protection: Defender Integration
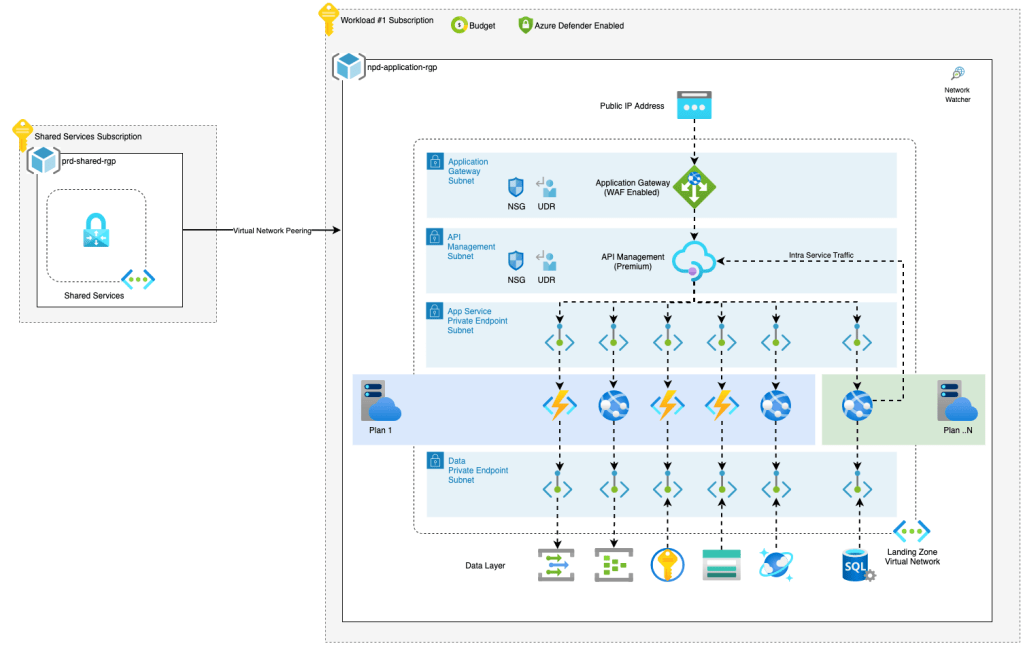
On the security side, Agent 365 integrates with Microsoft Defender for centralised threat detection and response. This goes beyond what we covered in the Content Safety post. This is runtime monitoring at the platform level.
What you get:
- Out-of-the-box threat detections: alerts on risky agent activities surfaced in Defender XDR
- Advanced hunting via KQL on the
CloudAppEventstable, so your SOC team can query agent activity alongside all your other security signals - Security posture management: understand agent attack paths and remediate misconfigurations
- Runtime defence: AI-powered blocking of prompt injection attacks and data exfiltration attempts in real time
Here’s a quick KQL example for hunting agent activity in Defender:
CloudAppEvents
| where ActionType in (
"InvokeAgent",
"InferenceCall",
"ExecuteToolBySDK",
"ExecuteToolByGateway",
"ExecuteToolByMCPServer"
)
| summarize count() by ActionType, bin(Timestamp, 1h)
| order by Timestamp descIf you’re already running Defender XDR, this is essentially free visibility into your agent estate. No new portal to learn.
The Developer Experience: SDK, CLI, and Blueprints
For developers building agents that need to play nicely with Agent 365 governance, Microsoft has shipped an SDK and CLI that adds enterprise capabilities to your existing agents.
Be warned: The SDK and CLI are currently in preview (you’ll need the --prerelease flag). But the developer experience is already pretty polished.
The CLI installs as a .NET global tool:
# Install the CLI
dotnet tool install --global Microsoft.Agents.A365.DevTools.Cli --prerelease
# Initialise configuration
a365 config init
# Full setup (registers blueprint, configures governance)
a365 setup all
# Deploy to Azure
a365 deploy
# Publish agent package to Agent 365
a365 publishThe SDK itself is available across .NET, Python, and JavaScript. Here’s how you’d add Agent 365 observability to an existing .NET agent using Semantic Kernel:
using Microsoft.Agents.A365.Observability;
using Microsoft.Agents.A365.Observability.Extensions.SemanticKernel;
var builder = WebApplication.CreateBuilder(args);
// Add Agent 365 tracing (OpenTelemetry-based)
builder.Services.AddAgenticTracingExporter();
// Auto-instrument Semantic Kernel
builder.Services.AddTracing(config => config.WithSemanticKernel());The key concept for developers is Agent Blueprints. A blueprint is an IT-approved, pre-configured agent type definition that specifies capabilities, MCP tool access, security constraints, audit requirements, and linked governance policies (DLP, external access restrictions, logging rules). Think of it as a template that ensures every agent instance inherits consistent governance.
The workflow is: IT creates blueprints with approved configurations. Developers build agents from those blueprints. Every instance inherits the blueprint’s governance rules automatically. This gives developers the freedom to build while giving IT the guardrails they need. No more rogue agents with unrestricted access.
What Does It Cost?
The licensing model is worth understanding because it’s different from what you might expect:
- $15 per user per month (standalone)
- Included in Microsoft 365 E7 ($99/user/month), which bundles M365 E5 + Copilot + Entra Suite + Agent 365
The important bit: licensing is per user, not per agent. All agents acting on behalf of a licensed user are covered. So if you have 100 licensed users and 50 agents serving them, you pay for 100 user licenses, not 50 agent licenses. For organisations running lots of agents, this is a much more predictable cost model than per-agent pricing would have been.
Note: You need at least one Microsoft 365 Copilot license to access Agent 365, even in the standalone plan. This is a prerequisite, not a bundle.
Currently in Frontier preview, with GA on May 1, 2026. Frontier participants get 25 free licenses valid through December 2026.
I want to be transparent here: the community reaction to the pricing has been mixed. Gartner called Agent 365 “a work in progress with limited net new functionality to justify its $15 pupm price point.” Paul Robichaux at Office 365 IT Pros cautioned against rushing into the E7 bundle, noting that only about 3% of the M365 installed base currently uses Copilot. And a recurring question on the Tech Community forums is whether Agent 365 delivers genuinely new functionality or bundles existing Purview, Defender, and Entra capabilities under a new SKU.
My take? It’s a bit of both. The individual capabilities (DLP, Insider Risk, Conditional Access) already exist. What Agent 365 adds is the agent-aware glue: the registry, the blueprints, the lifecycle policies, and the agent-specific policy templates. Whether that’s worth $15/user/month depends on how many agents you’re running and how seriously your compliance team takes AI governance. For organisations with a handful of agents, it might be premature. For enterprises with dozens of agents across multiple platforms, the centralised visibility alone starts to justify it.
The Elephant in the Room: Is It Actually Unified?
I’d be doing you a disservice if I didn’t mention this. Despite being marketed as a “unified control plane,” the admin experience today still involves bouncing between the M365 Admin Center, Entra ID, Purview, and SharePoint Advanced Management. AvePoint’s assessment described it as a “swivel-chair” experience, and I think that’s fair. Agent 365 provides the policy framework and data model that ties everything together, but the day-to-day admin UX is still distributed across multiple portals.
Microsoft is clearly working towards a single-pane experience, and the M365 Admin Center’s Agents section is the starting point. But if you’re expecting a single console that handles everything from agent discovery to DLP policy authoring to threat investigation, that’s not quite where we are yet. Think of it as the control plane that connects existing admin surfaces, not (yet) one that replaces them.
As Precio Fishbone put it, Agent 365 is “an overlay, not a replacement.” I think that’s the right mental model.
Wrapping Up
Agent 365 fills what was, in my opinion, the biggest gap in Microsoft’s agentic story: governance at scale. We’ve had the tools to build agents (Foundry, Copilot Studio), secure their identities (Entra Agent ID), protect their interactions (Content Safety), and evaluate their behaviour (Foundry Evaluators). What we didn’t have was a single place to discover, govern, and monitor all of them. Now we do.
If you’re running more than a handful of agents in production, or planning to, I’d strongly recommend getting into the Frontier preview before GA hits in May. The registry alone is worth the effort, and the Purview integration means you can extend your existing compliance posture to cover AI agents without building anything new.
As always, feel free to reach out with any questions or comments!
Until next time, stay cloudy!