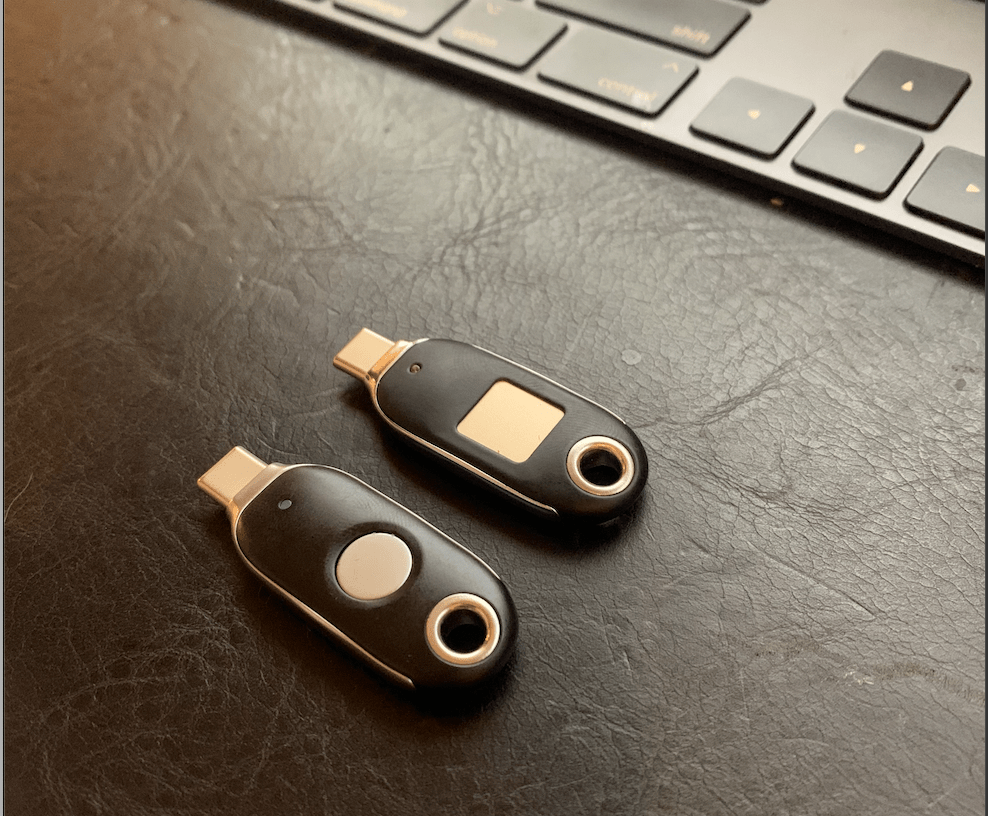
Recently I was lucky to receive some evaluation security keys from Feitian – One of the select companies currently providing Microsoft tested FIDO2 hardware. I’ve always been passionate about enabling Windows Hello for business, so the chance to get even more password-less was something I leaped at.
If you haven’t used a FIDO key before, the first things you will want to know are, what are they? how do I enable usage and how do I use them? Thankfully, the answer to these questions is pretty simple.
What is a FIDO2 Key?
Most people reading this post will currently maintain some form of password. The key detail being, this is generally a single password, maybe with a few permutations (hats off to the 1 in every 5 people using a password manager). These passwords are never very good – Hard to remember, simple to steal, easy to brute force and allowing massive re-use when stolen. FIDO is a solution to this nightmare.
FIDO as a concept is pretty easy to understand – You own a cryptographically verifiable key and this is used to authenticate on your services. Because FIDO allows you to physically own something with your security info, organisations can generate long & complex data, without you having to memorise it. Most importantly, this security data stays with you (sometimes even locked by your biometrics). Possession is nine tenths of the law and using FIDO it is much harder for malicious entities or hackers to break into your accounts.
As a protocol, FIDO has a fair bit of minutiae to understand. Microsoft provides an excellent summary within their existing password-less documentation. If you really enjoy long boring technical documents, the Technical Specs for FIDO2 from the FIDO alliance and W3C can be found here.
Enabling security key usage in Azure AD
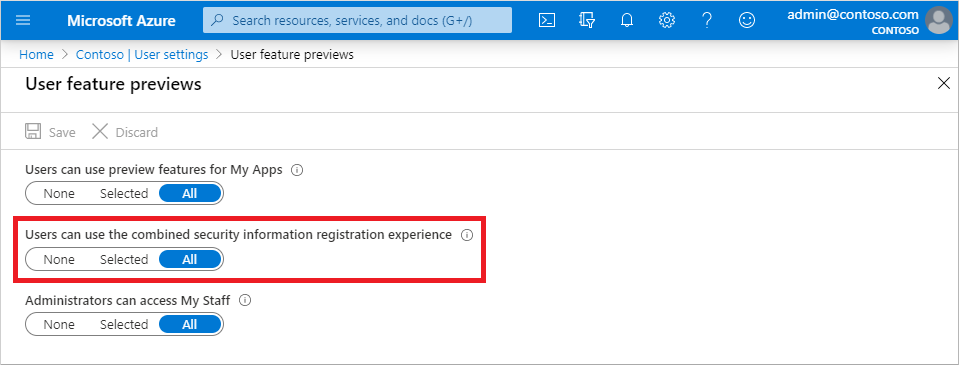
Enabling authentication within Azure AD is a pretty straight forward process. If you have an older AAD Tenant, you want to make sure that Combined Security registration is enabled. (On by default from August 15th 2020)
To do so, navigate to Azure AD user settings, and ensure the combined option is set to all users.
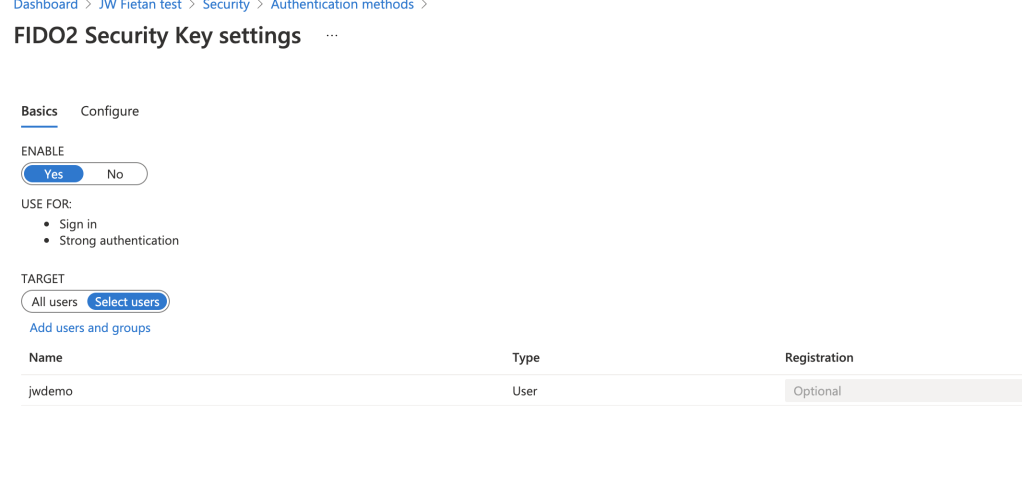
Next to enable security keys, navigate to Security > Authentication Methods
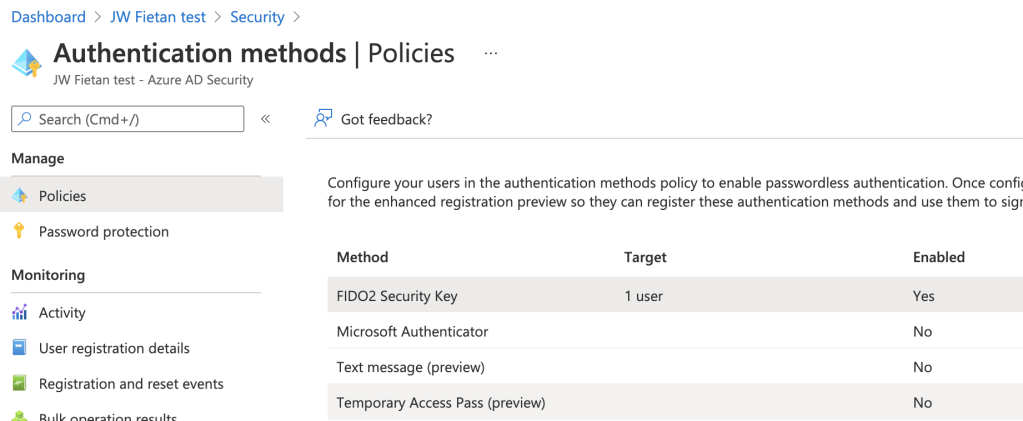
By selecting FIDO2 Security Key you can enable this authentication method for a select group or all users. There isn’t any major penalty for enabling this on all users, however if completing this task under a dedicated rollout, you may want to consider who should have a key OR if you wanted to configure allowed AAGUIDs using data provided from your manufacturer.
Setting up and using a key
Now that we’ve enabled the service, it’s time for the part we are all keen for – actually using a key! To do so, plug your security key into your pc. Next, I would recommend installing the relevant configuration software for your device. This allows you to configure any settings available in your key.
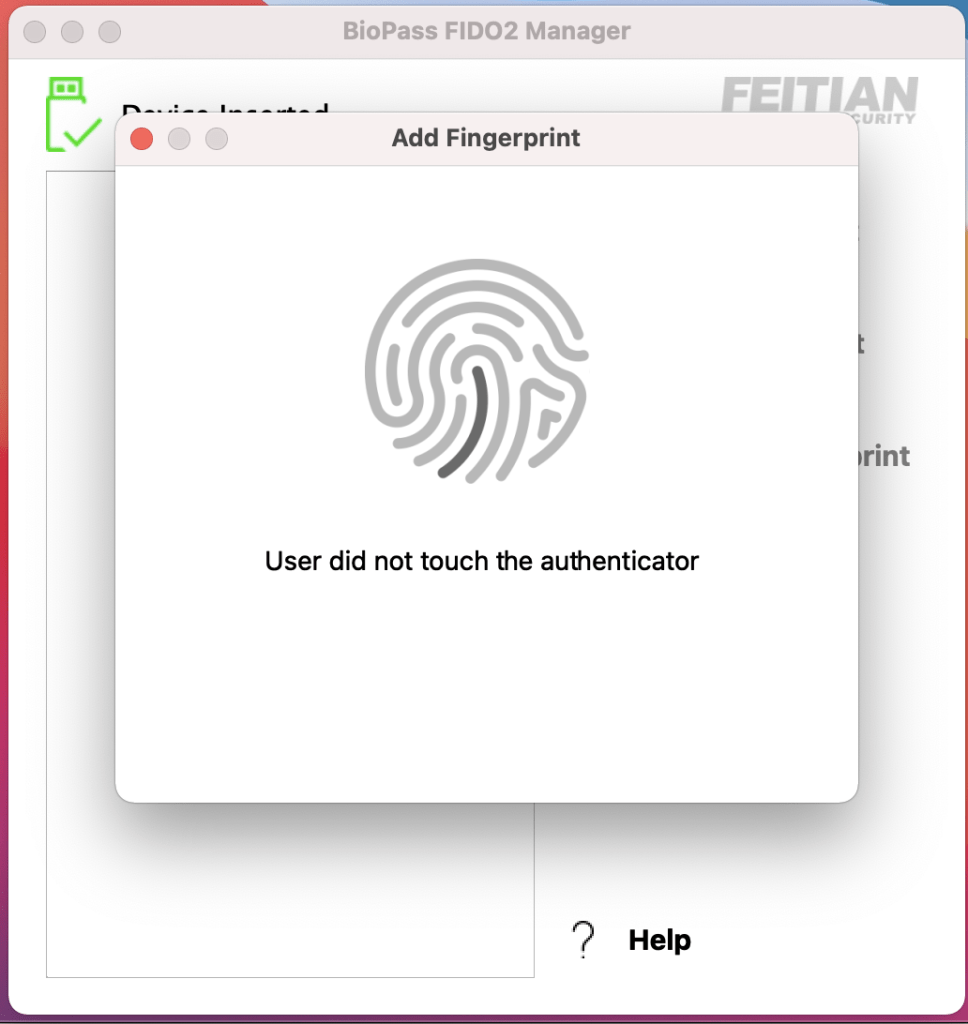
In the case of my FEITIAN K26 key, I have an option to configure an extra biometric – My Fingerprint. This is great, as I’m now protecting the access that this key grants with my unique properties!
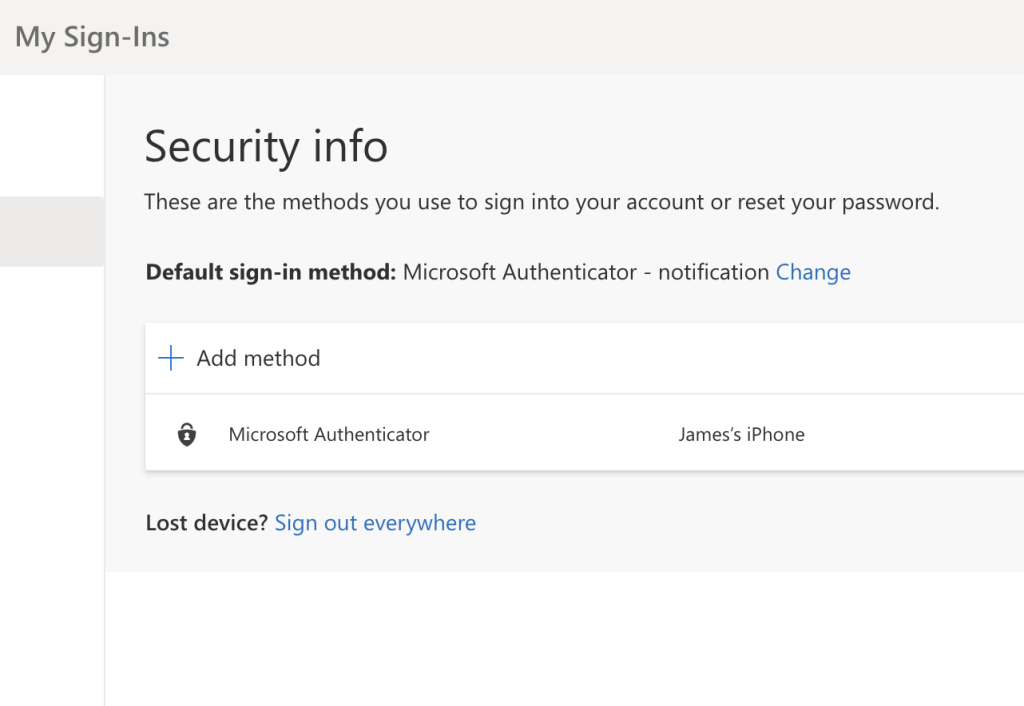
Once you’ve configured your key settings, it’s time to connect this to Azure AD. Complete a login into the MyApps portal. From here, you can use the security settings page to add the FIDO key for use.
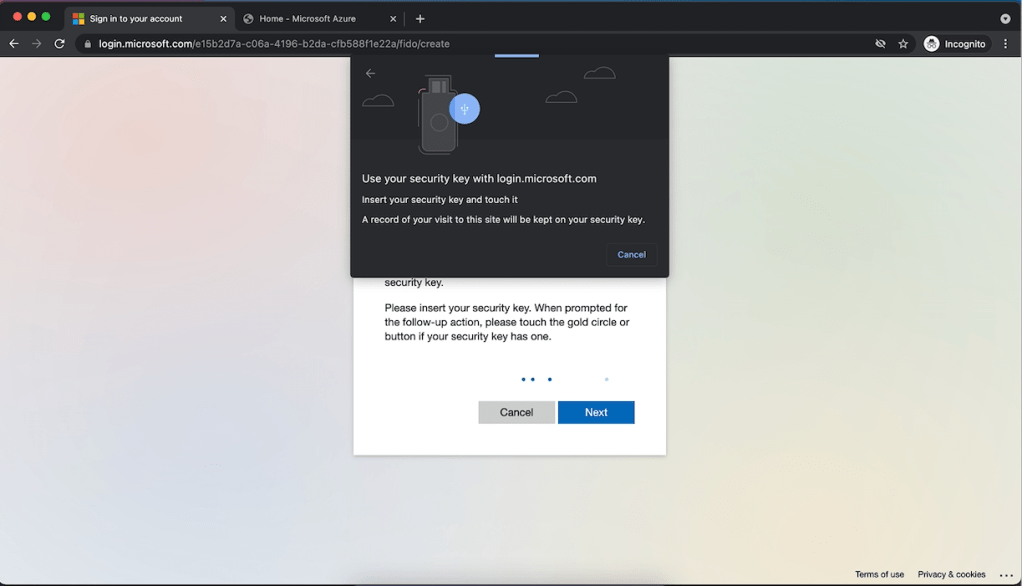
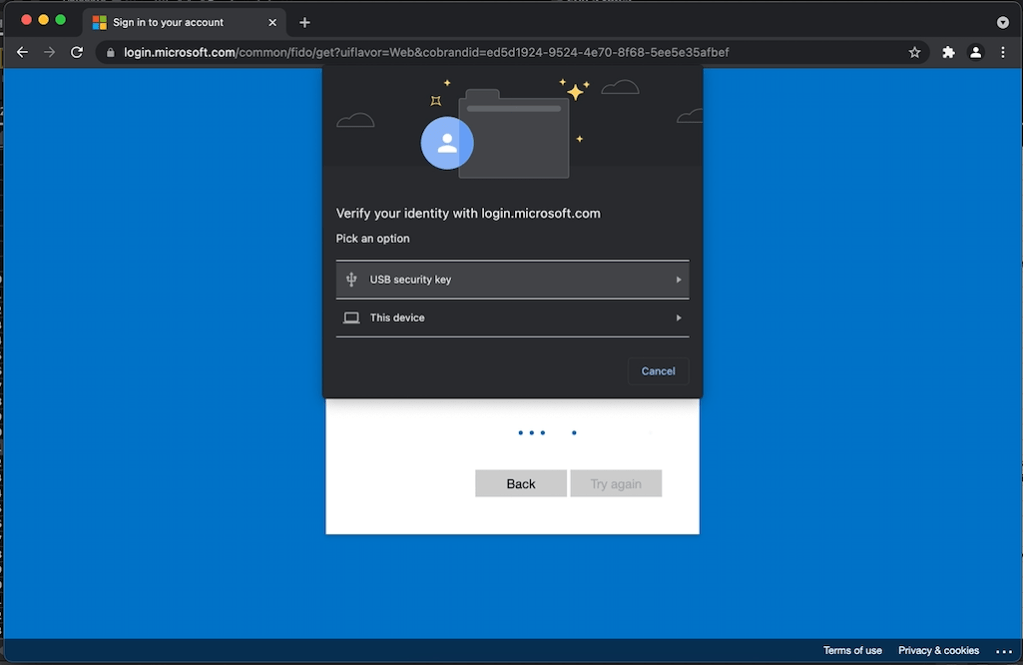
Once setup, your next login should have the option to login with a security key!
A few weeks with my keys
After spending some time using these security keys, I’m thoroughly enjoying the change. They simplify login and provide me with a degree of confidence in my account security. As far as product feedback goes, I have had no issues with the FEITIAN keys – Just personal nigglings which will vary between users. The build quality is great, with the inbuilt loops letting me easily attach to my keys for on the go use. I accepted two USB C devices, which I surprisingly found challenging. As a Mac user, Apple has pushed a lot of my devices to USB-C. I thought I was all done with USB 2.0, but didn’t really think of my corporate devices, meaning I wasn’t able to use the keys there. Form factor wise, the devices could be a bit smaller, with the larger keys being a little bit concerning when moving my laptop around. I was really worried I would snap one off. FEITIAN offers the K21, K28 keys with a slimline build, so next time I might grab a pair of those!
A big Thank you to Della @ FEITIAN for the opportunity to test these keys, until next time – Stay cloudy!