Microsoft consolidated Azure AI Studio, Azure AI Foundry, and Azure OpenAI into a single platform called Microsoft Foundry. Here’s the rebrand lineage, what actually changed architecturally, and what the migration path looks like.More
The Responses API: Azure OpenAI’s New Core Interface, and Why It Replaces Everything You Know
Azure OpenAI’s Responses API unifies Chat Completions and the Assistants API into a single stateful interface with built-in tools, context compaction, and remote MCP support. Here’s what changed, why it matters, and how to migrate.More
Azure Spring Clean – 5 Tips to help you align to Enterprise Scale
In this post I discuss 5 tips which you can easily implement to align to Microsoft’s Enterprise Sale Landing Zone guidance. More
GitHub Advanced Security – Exporting results using the Rest API
In this post I explain how to export GitHub Advanced Security results using the REST API and PowerShell. More
Securing Privileged Access with Azure AD (Part 3) – Hybrid Scenarios
Ensuring that privileged access is managed in your organisation is a critical step within any holistic cybersecurity program. This is the third post in a series explaining how to secure Privileged Access using Azure AD features and integrations. More
Easy management of Github Wikis with Actions
In this post I discuss a simple action to manage GitHub wiki’s using Actions. More
Enabling Password-less in Azure AD with Feitian security keys!
Recently I was lucky to receive some evaluation security keys from Feitian – One of the select companies currently providing Microsoft tested FIDO2 hardware. I’ve always been passionate about enabling Windows Hello for business, so the chance to get even more password-less was something I leaped at. If you haven’t used a FIDO key before,…More
Securing Privileged Access with Azure AD (Part 2) – The AAD Basics
Ensuring that privileged access is managed in your organization is a critical step within any holistic cybersecurity program. This is the second post in a series explaining how to secure Privileged Access using Azure AD features and integrations. More
Securing Privileged Access with Azure AD (Part 1) – Strategy and Planning
Ensuring that privileged access is managed in your organisation is a critical step within any holistic cybersecurity program. This is the first post in a series explaining how to secure Privileged Access using Azure AD features and integrations. More
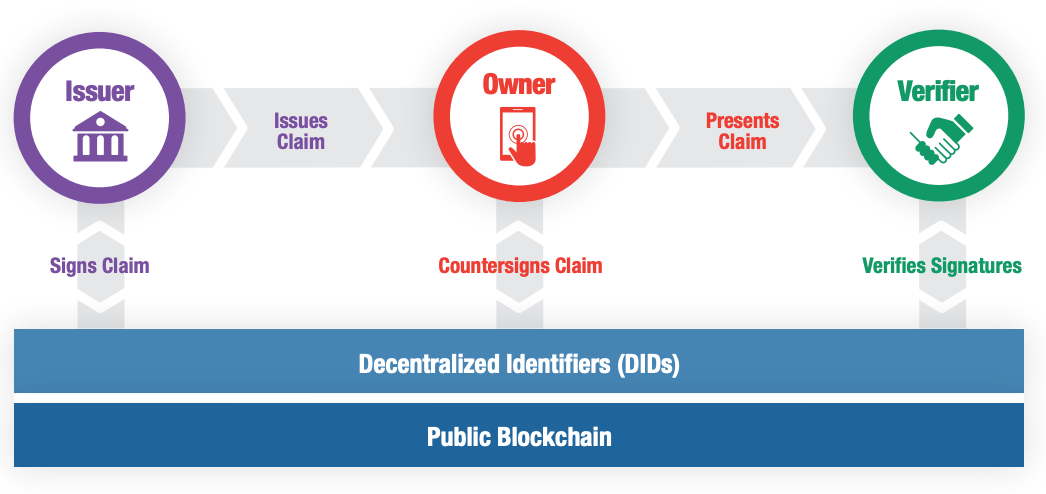
A first look at Decentralised Identity
In this post I explain what decentralised identity is, the challenges it solves and the new Azure AD solution, Verifiable Credentials. More